Even though we have been neglecting the News pages a bit these past few months, it does not mean nothing has happened.
So here is a short summary of awards we have won since 2021:
- Paranoid Android: Versatile Protection For Smartphones, published t ACSAC 2010 won the Test of Time Award in 2025
- InSpectre Gadget: Inspecting the Residual Attack Surface of Cross-privilege Spectre v2. USENIX Security, August 2024. Distinguished paper award
- SafeFetch: Practical Double-Fetch Protection with Kernel-Fetch Caching,USENIX Security’24, distinguished Artifact Award
- Uncontained: Uncovering Container Confusion in the Linux Kernel, USENIX Security’23 won distinguished artifact award.
- Specification and Verification of Side-channel Security for Open-source Processors via Leakage Contracts, CCS’23 won distinguished paper award.
- Randomized Testing of Byzantine Fault Tolerant Algorithms, OOPSLA’23 won distinguished paper award
- Branch History Injection: On the Effectiveness of Hardware Mitigations Against Cross-Privilege Spectre-v2 Attacks, USENIX Security’22, won the Dutch Cyber Security Research Paper Award
- Our ASPLOS paper “Who’s debugging the debuggers?” was awarded a Distinguished Paper Award!
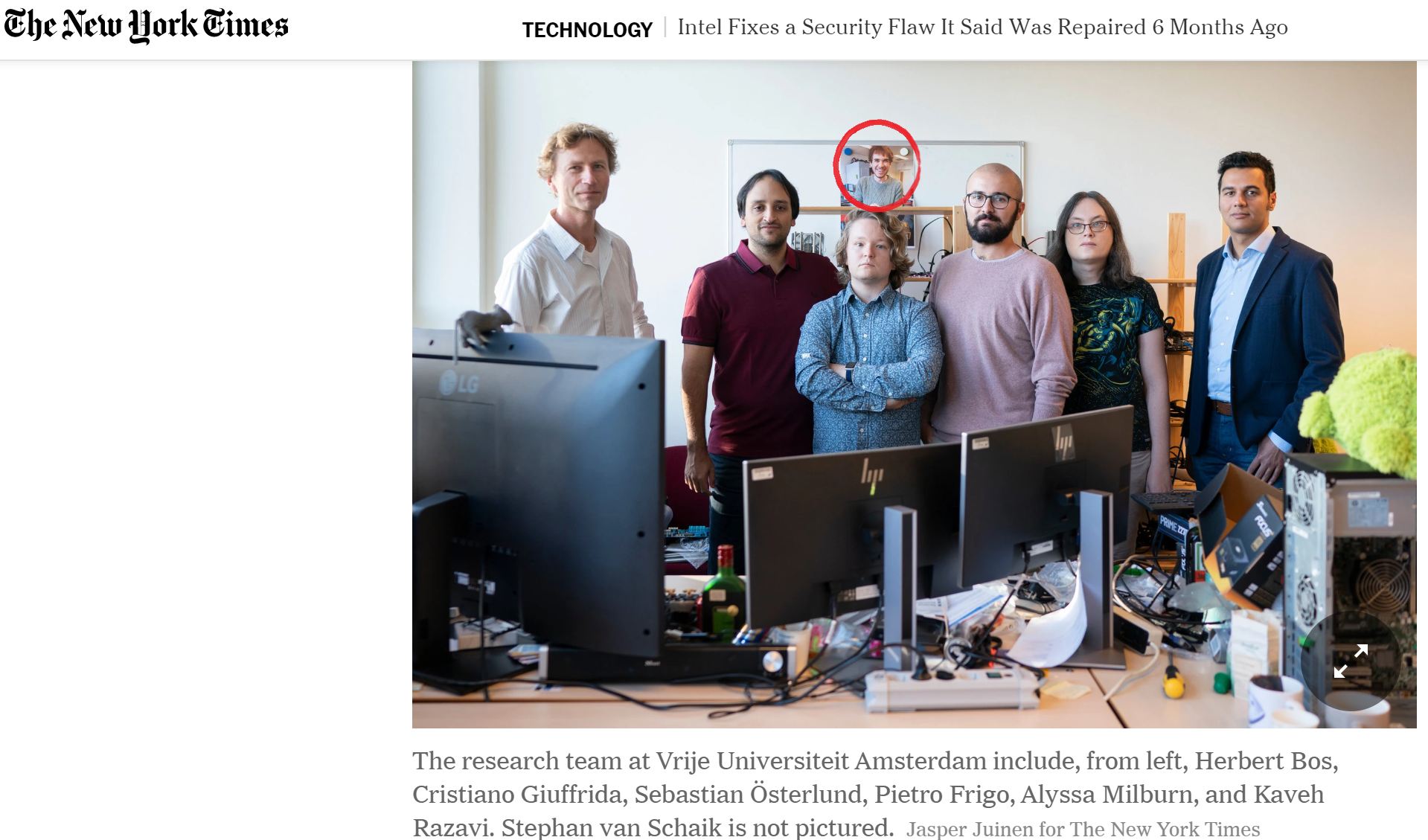
- Victor van der Veen from won the 2021 EuroSys Roger Needham Ph.D. Award for his thesis titled “When Memory Server Not so Well: Memory Errors 30 Years Later“.
- VUsec was nominated for 6 Pwnie Awards
- Enes Goktas’ BlindSide (“hacking blind” in the Spectre era) Attack won Pwnie for Most Innovative Research (VUSec’s 5th Pwnie Awards)
- Victor van der Veen from won the 2021 DSN William C Carter Doctoral Dissertation Award for his thesis titled “When Memory Server Not so Well: Memory Errors 30 Years Later“.
- Our paper, “Rage Against the Machine Clear: A Systematic Analysis of Machine Clears and Their Implications for Transient Execution Attacks“, won Distinguished Paper Award at USENIX Security’21.